Greasy Fork is one of the most popular platforms for sharing and downloading user scripts, but with that popularity comes an important question: is it actually safe to use? Whether you’re looking to customize websites, remove ads, or add powerful new features to your browser, Greasy Fork can seem like a goldmine. However, because it hosts community-created scripts, there are real security and privacy considerations you should understand before clicking “install.”
TLDR: Greasy Fork itself is generally safe and actively moderated, but the scripts hosted on it are created by users and can pose security and privacy risks. Most scripts are harmless and useful, yet malicious or poorly coded ones can steal data, inject ads, or compromise accounts. Always check reviews, permissions, and source code before installing. With smart precautions, Greasy Fork can be a valuable and safe tool.
In this guide, we’ll break down how Greasy Fork works, the potential security risks involved, how to evaluate script safety, and the practical steps you should take to protect yourself.
What Is Greasy Fork and How Does It Work?
Greasy Fork is a website that hosts user scripts—small pieces of JavaScript code that modify how websites behave in your browser. These scripts are typically installed using browser extensions like:
- Tampermonkey
- Violentmonkey
- Greasemonkey
Once installed, a user script runs when you visit specific websites. For example, a script might:
- Remove ads from a site
- Add download buttons to platforms that don’t have them
- Automate repetitive tasks
- Improve layouts or dark mode features
- Display hidden data
The power of these scripts is what makes Greasy Fork appealing—but also what makes it potentially risky. They can manipulate webpages at a deep level, sometimes accessing login sessions and personal data.
Is Greasy Fork Itself Safe?
Let’s separate the platform from the scripts.
The platform:
- Greasy Fork has active moderation.
- It has clear policies against malicious scripts.
- It displays source code publicly for transparency.
- It allows users to report suspicious scripts.
From a platform perspective, Greasy Fork is considered relatively safe. It is designed around transparency and open code, which allows scrutiny from the community.
The scripts:
- Created by individual developers.
- Can be updated at any time by the author.
- May request broad permissions.
- Are not always professionally reviewed.
This is where the real risk lies. Because scripts are user-generated, their safety depends entirely on the developer’s intent and competence.
Security Risks of Using Greasy Fork Scripts
Here are the main risks you should be aware of:
1. Data Theft
Since scripts run in your browser, they may have access to:
- Cookies
- Session tokens
- Form inputs
- Page content
A malicious script could capture login credentials or sensitive information and send it to a remote server.
2. Account Takeover
If a script has access to authenticated sessions (for example, your social media account or email), it might perform actions on your behalf. This could include posting spam, changing settings, or scraping private data.
3. Hidden Cryptocurrency Mining
Though less common today, some scripts in the broader web ecosystem have secretly used device resources to mine cryptocurrency, slowing down computers significantly.
4. Injection of Ads or Redirects
A script might secretly:
- Insert affiliate links
- Replace legitimate ads with the author’s ads
- Redirect you to malicious websites
5. Poor Coding Practices
Not all issues are intentional. Some developers:
- Fail to properly secure network requests
- Expose sensitive data accidentally
- Create conflicts with other extensions
Even a well-meaning developer can unintentionally create vulnerabilities.
How to Tell If a Script Is Safe
Before installing any script, take the following steps:
Check the Author’s Reputation
- How many scripts has the author published?
- Do they have positive feedback?
- Are their scripts widely used?
An established profile with multiple well-reviewed scripts is generally safer than a brand-new account with no history.
Look at Install Counts and Reviews
While not foolproof, high install numbers and positive user comments are good indicators. Watch for:
- Recent complaints
- Reports of suspicious behavior
- Mentions of data leaks
Review Permissions Carefully
Check which domains the script can access. If a script meant to modify one website requests access to all websites, that’s a red flag.
Read the Source Code (If You Can)
Even if you aren’t a programmer, you can look for obvious warning signs like:
- Mysterious external URLs
- Obfuscated (intentionally unreadable) code
- Frequent calls to unknown servers
Greasy Fork requires scripts to be reasonably readable, which helps reduce hidden threats—but doesn’t eliminate them entirely.
Comparing Popular Script Managers
Safety doesn’t only depend on Greasy Fork. Your script manager also matters. Here’s a comparison:
| Feature | Tampermonkey | Violentmonkey | Greasemonkey |
|---|---|---|---|
| Ease of Use | Very user friendly | Simple and lightweight | Basic interface |
| Performance | High | Very high | Moderate |
| Open Source | No (partially closed) | Yes | Yes |
| Automatic Updates | Yes | Yes | Yes |
| Security Controls | Granular permissions | Strong isolation | Limited advanced controls |
While all three are widely used, Violentmonkey and Greasemonkey are fully open source, which some users prefer from a transparency standpoint.
Best Practices for Staying Safe
If you want to minimize risks while using Greasy Fork, follow these smart habits:
1. Install Only What You Need
The more scripts you install, the larger your attack surface becomes. Keep your setup minimal.
2. Use a Secondary Browser
Consider installing scripts in a separate browser profile. Avoid running experimental scripts in the same browser you use for:
- Online banking
- Work accounts
3. Regularly Review Installed Scripts
Remove scripts you no longer use. Old or abandoned scripts can become security risks if they stop receiving updates.
4. Disable Scripts on Sensitive Sites
Many script managers allow you to control where scripts run. Avoid letting them execute on financial or highly sensitive websites.
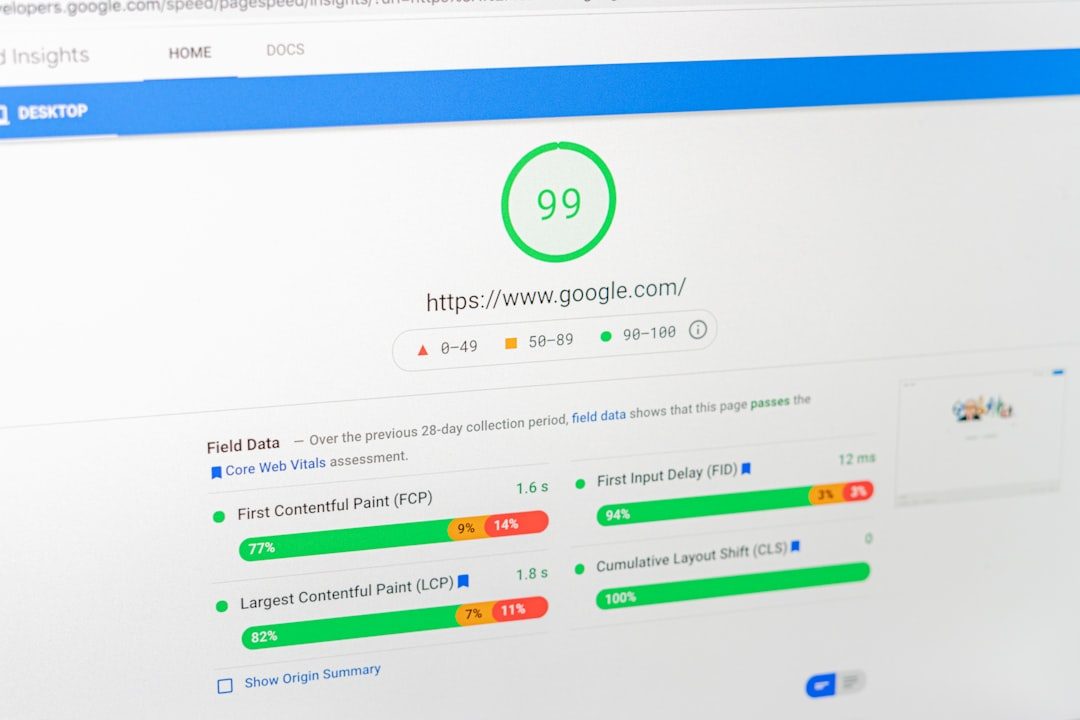
5. Monitor Network Activity (Advanced Users)
Tech-savvy users can inspect browser developer tools to check for suspicious outgoing network requests.

Are There Alternatives to Greasy Fork?
Yes, though they carry similar risks. Alternatives include:
- OpenUserJS
- Direct GitHub script repositories
- Private developer websites
However, Greasy Fork is often considered safer than random downloadable scripts from unknown websites because:
- It enforces code visibility.
- It has active moderation.
- It allows user reporting.
Common Myths About Greasy Fork
“All Scripts Are Dangerous”
False. Most scripts are created to solve genuine usability frustrations. The majority function exactly as advertised.
“If It Has Thousands of Installs, It’s 100% Safe”
Not necessarily. Popular scripts can still contain vulnerabilities, especially after updates.
“Open Source Means Completely Safe”
Open source improves transparency but doesn’t guarantee someone has audited the code carefully.
The Bottom Line: Is Greasy Fork Safe?
Greasy Fork is generally safe as a platform, but not risk-free. The real variable is the script you install. Because these scripts can deeply interact with websites and your data, they deserve the same caution you would apply to installing any browser extension.
If you:
- Research the author
- Read user feedback
- Review permissions carefully
- Limit access to sensitive sites
- Remove unused scripts regularly
—you can dramatically reduce your exposure to threats.
For everyday users who practice reasonable caution, Greasy Fork can be a powerful way to take control of the web experience. For careless users who install everything without reviewing details, it can become a security liability.
Like many tools online, Greasy Fork isn’t inherently dangerous—it’s powerful. And with power comes responsibility.